Introduction
In the vast expanse of the digital universe, where lines of code drive our everyday lives, there lurk enigmatic figures known as the “Ghost Coders.” These are the individuals or groups who, shielded by layers of anonymity, create some of the most infamous and disruptive viruses the world has ever seen. Their creations often wreak havoc, causing financial damages in the billions, and occasionally, their digital footprints even influence global geopolitics. But who are these mysterious entities? Why do they do what they do? This article aims to delve deep into the shadows, shedding light on the anonymous figures behind the world’s most notorious digital threats.
The Lure of Anonymity
In the world of hacking and malware creation, anonymity isn’t just a luxury—it’s a necessity. The reasons driving coders to cloak their identities are multifaceted and vary from individual to individual.
Fear of legal repercussions is a significant factor. Global law enforcement agencies are continually on the prowl, aiming to bring cybercriminals to justice. Being identified could mean long prison sentences, hefty fines, or even extraditions to countries with stringent cyber laws.
Yet, for many, there’s a deeper allure. The desire for notoriety without personal consequences is compelling. By remaining faceless, these coders gain infamy in the digital underworld and among cybersecurity experts, becoming legends whispered about in hushed tones. Their viruses, worms, or ransomware are their signatures—calling cards that announce their prowess to the world, all while keeping their true identities shrouded in mystery.
And then, there’s the sheer thrill of the challenge. For some ghost coders, the act of creating and releasing a virus is akin to an intricate game of chess. They revel in outsmarting security experts, infiltrating systems, and watching the digital dominos fall, all from the shadows of their anonymous vantage point.
The Evolution of Digital Viruses
When we reminisce about the early days of the digital age, viruses might seem like simple, almost benign nuisances. But as the digital landscape evolved, so did these virtual threats, growing in sophistication and malevolence.
Early Beginnings: More Prank Than Peril The inception of computer viruses was often rooted in curiosity rather than malice. Early examples include the Elk Cloner, which was more of a playful jab at Apple II users, displaying a cheeky poem after every 50th boot. Similarly, the Brain virus, often cited as the first PC virus, was created by two Pakistani brothers, not to damage, but rather to safeguard their software from piracy.
The Tidal Shift: Malice and Motives However, as the potential for financial gains became evident, the nature of viruses underwent a seismic shift. No longer were they just digital pranks. Viruses started targeting financial systems, stealing data, and extorting money. Ransomware, like the infamous CryptoLocker, didn’t just lock users out of their data but demanded ransoms in cryptocurrencies, a trend that has only amplified with time.
Furthermore, the world began witnessing cyberattacks with political motivations. Nation-states realized the potential of using viruses as cyber weapons, and thus, digital warfare took a front seat in geopolitics. Attacks were no longer just about individual gains but about national interests, power dynamics, and political leverage.
Modern Monsters: Viruses with Global Impacts Today’s viruses are multifaceted beasts. While some are still rooted in financial or personal gains, others have the capability to disrupt national grids, influence elections, or even cripple entire industries. The tools and techniques have evolved, but so has the defense against them. Yet, the challenge remains: as fast as security patches are released, ghost coders find another loophole, another vulnerability, ensuring their continued relevance in this ever-evolving digital dance.
Profiles of the Most Infamous Viruses
The world of cyberthreats is vast and varied, but certain viruses stand out for their audacity, intricacy, and the sheer scale of destruction they caused. Delving into these infamous viruses provides insights not just into their architecture but also into the minds of the ghost coders who crafted them.
Stuxnet: The Silent Saboteur
- Origins and Speculated Creators: Emerging from the shadows in 2010, Stuxnet wasn’t just another virus—it was a cyber weapon. Its sophistication suggested that it wasn’t the work of a lone wolf but rather a coordinated effort, possibly even backed by nation-states. While never officially confirmed, whispers among the cybersecurity community point towards a collaboration between the U.S. and Israel.
- Target and Impact: Rather than casting a wide net, Stuxnet had a very specific target: the nuclear facilities in Iran. By exploiting vulnerabilities in the software controlling the centrifuges, it managed to cause significant physical damage, slowing down the country’s nuclear ambitions without ever dropping a traditional bomb.
- Legacy: Stuxnet opened the world’s eyes to the potential of cyber warfare. It wasn’t just about digital damage anymore; cyberattacks could have tangible, real-world consequences.
WannaCry: The Global Blackmailer
- Rapid Spread and Chaos: In May 2017, the world woke up to the chaos caused by WannaCry ransomware. Within hours, it spread across 150 countries, locking out users from their data and demanding Bitcoin ransoms.
- Victims and Vulnerabilities: No one was safe. From hospitals in the UK to factories in France and railways in Germany, the ransomware exploited a Windows vulnerability, causing widespread disruption.
- Global Response: What was unique about WannaCry’s reign of terror was the concerted global effort to stop it. Cybersecurity experts from different corners of the world collaborated in real-time, ultimately finding a “kill switch” to halt its spread.
- Aftermath and Lessons: Beyond the immediate financial damage, WannaCry highlighted the need for regular software updates and the dangers of using outdated systems.
Mydoom: The Speed Demon
- Unprecedented Propagation: Released in 2004, Mydoom became the fastest-spreading email worm in history. Within a single day, one out of every 12 emails was infected, causing email systems to grind to a halt.
- Origins and Theories: The primary motive behind Mydoom seemed to be a Distributed Denial of Service (DDoS) attack against a few targeted websites. However, the creator’s identity and the exact reasons for the attack remain shrouded in mystery. Some theories hint at a Russian origin, while others believe it might have been commissioned by rival companies.
- Legacy and Evolution: While Mydoom caused immediate and palpable disruptions, its true legacy lies in the subsequent variants and mutations it inspired. Ghost coders took note of its effectiveness, leading to a slew of similar attacks in the following years.
The vast and varied landscape of viruses, from Stuxnet’s precision targeting to WannaCry’s indiscriminate spread and Mydoom’s record-breaking speed, offers a window into the world of ghost coders. Their motivations, techniques, and goals might differ, but their ability to shape and challenge the digital realm remains a constant. These viruses, and the minds behind them, serve as a testament to the ever-evolving game of cat and mouse that defines our digital age.
The Role of the Dark Web
The Dark Web, often depicted as the nefarious underbelly of the internet, plays a pivotal role in the realm of ghost coders. Beyond its portrayal in pop culture, the Dark Web is a complex ecosystem that both shields and sustains these elusive figures.
A Haven for Ghost Coders
- Platforms of Exchange: The Dark Web hosts numerous forums and marketplaces where ghost coders can sell, buy, or exchange malware, ransomware, and other malicious tools. These platforms often operate on a reputation system, ensuring the reliability of transactions.
- Communication Hubs: Beyond transactions, the Dark Web serves as a space for these coders to share knowledge, collaborate on projects, and discuss potential vulnerabilities or targets. It’s a community bound by secrecy and a shared passion for hacking.
Tools of Anonymity
- Tor and Its Layers: At the heart of the Dark Web lies the Tor network, a system that allows users to access websites anonymously. By routing internet traffic through multiple volunteer-run servers, Tor ensures that users’ locations and usage remain concealed.
- VPNs: The Double Cloak: Virtual Private Networks (VPNs) add another layer of anonymity. When combined with Tor, it becomes exceedingly difficult for even seasoned investigators to trace activities back to their source.
- Cryptocurrency: The Anonymous Transaction: Traditional banking systems leave traces, digital footprints that can be followed. Cryptocurrencies, with their decentralized nature, offer ghost coders a way to conduct financial transactions without revealing their identities.
The Ethical Dilemma
- Not All Darkness: Contrary to its reputation, not everything on the Dark Web is illegal or malicious. Many use it to bypass censorship, access restricted information, or simply ensure privacy in an age of surveillance.
- The Fine Line: While it harbors and aids ghost coders, the Dark Web also provides essential services to activists, journalists, and others living under oppressive regimes. It’s a reminder of the nuanced nature of this hidden realm.
Challenges for Law Enforcement
- A Game of Whack-a-Mole: As soon as one Dark Web marketplace is shut down, another springs up. The decentralized and anonymous nature of the Dark Web makes it a challenging space for law enforcement to monitor and control.
- International Cooperation: The global nature of the Dark Web requires international collaboration for any significant crackdown. Jurisdictional challenges and varying cyber laws across countries can often hamper coordinated efforts.
The Dark Web, with its maze-like structure and ethos of absolute anonymity, is an indispensable ally for ghost coders. Yet, it’s essential to remember that like any tool, its value lies in the hands of the user. While it may shield those with malicious intent, it also protects those fighting for freedom, rights, and justice in the digital age.
Unmasking the Ghosts
The cyber realm is a vast, intricate web of codes, systems, and digital footprints. And while ghost coders are experts at evading detection, there have been instances where these digital phantoms were dragged into the light. These tales of unmasking not only demonstrate the resilience of cybersecurity professionals but also the vulnerabilities even the best coders can’t always hide.
The Pursuit of Shadows
- Digital Detectives: Cybersecurity experts and digital forensics teams are the detectives of the digital age. Using a combination of tools, techniques, and sometimes even old-fashioned detective work, they piece together the puzzles left behind by ghost coders.
- Patterns and Profiles: Just as traditional criminals might have a modus operandi, ghost coders too can fall into patterns, favoring certain codes or techniques. Identifying these patterns can lead experts to the culprits.
Notable Unmaskings
- The Blackshades Takedown: A malware that allowed users to remotely control other computers, Blackshades, was a favorite among cybercriminals. Its creator, Alex Yucel, might have remained anonymous if not for a global effort involving 19 countries that eventually led to his arrest and conviction.
- Guccifer 2.0 Exposed: Initially posing as a lone Romanian hacker, Guccifer 2.0 claimed responsibility for hacking the Democratic National Committee in 2016. However, meticulous analysis by cybersecurity firms linked the figure to Russian military intelligence, shattering the lone-wolf narrative.
The Dual-Edged Sword of Technology
- Evolving Anonymity Tools: As technology advances, so do the tools available for maintaining anonymity. While these tools make the task of unmasking harder, they can sometimes become the very weak points that expose the user.
- Shared Vulnerabilities: Ghost coders and cybersecurity experts often operate on the same technological plane, using similar tools and resources. This shared space means that while ghost coders exploit vulnerabilities, they can be susceptible to them as well.
Beyond the Mask
- Facing Consequences: Once unmasked, these coders face a myriad of legal consequences, ranging from international trials to lengthy prison sentences. Their tales serve as cautionary reminders of the risks lurking behind the veil of anonymity.
- Changing Allegiances: Interestingly, some unmasked individuals transition from being threats to assets. By collaborating with law enforcement or cybersecurity firms, they leverage their skills for legal and often lucrative avenues, trading their phantom masks for more public personas.
Wrapping the Shadows: As the digital landscape continues to evolve, the dance between ghost coders and those trying to unmask them will only grow more intricate. Each tale of unmasking serves as both a victory for the digital guardians and a testament to the ever-present challenge of maintaining anonymity in a connected world.
Preventing the Phantoms: Proactive Measures Against Cyber Threats
In the face of these formidable ghost coders, it becomes crucial for individuals, businesses, and nations to adopt a proactive approach. By understanding the methods employed by these anonymous figures and integrating comprehensive protective measures, we can minimize their potential impact and stay one step ahead.
Educate to Inoculate
- Awareness Campaigns: Often, the most significant vulnerability isn’t a software glitch but human error. Awareness campaigns can educate people on the dangers of phishing emails, the importance of regular software updates, and the perils of weak passwords.
- Training Programs: For businesses, ensuring employees are trained in cybersecurity basics can drastically reduce the risk of a breach. From recognizing suspicious links to securing personal devices, education is the first line of defense.
Implementing Robust Security Protocols
- Multi-factor Authentication: By requiring more than one method of verification, MFA makes unauthorized access significantly more challenging, even if passwords are compromised.
- Regular Backups: Ransomware attacks can hold data hostage. Regular backups, especially offsite or on cloud platforms, ensure data recovery without yielding to extortion.
- Continuous Monitoring: Real-time monitoring of networks can detect and neutralize threats before they wreak havoc. Automated systems paired with human oversight form a potent defense mechanism.
Staying Updated
- Software Patching: Keeping all software, especially operating systems and security software, updated ensures that known vulnerabilities are patched.
- Staying Informed: Cyber threats evolve rapidly. By staying informed about the latest threats and countermeasures, both individuals and businesses can adapt their defenses accordingly.
Collaborative Defense
- Sharing Threat Intelligence: Companies and nations can benefit from sharing information on new threats or vulnerabilities. Collaborative defense mechanisms, where knowledge of one breach can protect many, can be especially potent against organized cyber threats.
- Public-Private Partnerships: The combined resources of government agencies and private enterprises can lead to comprehensive defense strategies, research into advanced protective measures, and rapid responses to emerging threats.
Future-Proofing Through Innovation
- Investing in R&D: The future of cybersecurity lies in continuous innovation. Be it quantum encryption, AI-driven defense mechanisms, or blockchain-based security protocols, staying ahead of ghost coders means constantly pushing the technological envelope.
- Encouraging Ethical Hacking: Ethical hackers, or “white hat” hackers, use their skills to identify and fix vulnerabilities. Encouraging this practice through rewards or competitions can turn potential threats into allies in the fight against cybercrime.
In the Digital Fortress: As the stakes in the digital realm continue to escalate, proactive measures become our fortress against the specters of the cyber world. By fostering a culture of vigilance, collaboration, and innovation, we can ensure that the ghost coders remain mere shadows, unable to breach the walls of our collective defenses.
Ghost Coders in Pop Culture: Fiction Mirroring Reality
The allure of the hidden figures crafting complex viruses, the battles in the vast digital realm, and the intrigue of the unseen has not been lost on pop culture. Books, movies, TV shows, and even video games have drawn inspiration from these digital phantoms, blending fact with fiction and adding layers to the public’s understanding—or sometimes, misunderstanding—of these mysterious figures.
The Silver Screen’s Digital Outlaws
- “Hackers” (1995): One of the earliest cinematic ventures into the world of hacking, this film showcased a group of young hackers battling an evil mastermind. While not entirely accurate in its portrayal, it cemented hacking into popular culture.
- “Blackhat” (2015): Directed by Michael Mann, this film dove into the intricacies of cyber warfare, tracing a convict’s journey as he is released to help track down cybercriminals.
Literary Dives into the Digital Abyss
- “Neuromancer” by William Gibson: A seminal work in the cyberpunk genre, this novel introduced readers to a world of AI, hacking, and digital espionage long before these concepts became mainstream.
- “Ghost in the Wires” by Kevin Mitnick: An autobiography of one of the most notorious hackers turned security consultant, this book offers a firsthand look into the life of someone who once operated in the shadows.
Television’s Glimpse into the Matrix
- “Mr. Robot”: A critically acclaimed series that follows a cybersecurity engineer and vigilante hacker. Its realistic portrayal of hacking and the psychological impacts of living in the digital age has made it a touchstone in pop culture discussions on cybersecurity.
- “CSI: Cyber”: An offshoot of the popular CSI franchise, this show delved into the world of cybercrimes, bringing the concept of digital forensics to mainstream audiences.
Gaming’s Interactive Foray
- “Watch Dogs” Series: These video games allow players to step into the shoes of hackers, using their skills to navigate a city’s interconnected digital infrastructure, turning the virtual environment into both a playground and a weapon.
The Duality of Representation
- Glorification vs. Reality: While pop culture often glorifies hackers as rebellious heroes or mastermind villains, the reality can be more mundane. Not all ghost coders are out to change the world or amass riches; some are driven by curiosity, necessity, or even coercion.
- Educating or Misleading?: While these media portrayals can raise awareness about cybersecurity, they can sometimes perpetuate myths or oversimplify complex topics. It’s crucial for consumers to discern fiction from fact.
Dancing with Digital Shadows: Pop culture’s fascination with ghost coders and the digital realm underscores the profound impact of the cyber world on our collective consciousness. As stories continue to be woven around these enigmatic figures, they serve as both a reflection of society’s fears and a testament to our endless curiosity about the unknown.
The Evolution of Ghost Coders: Past, Present, and Future
To truly understand the phenomenon of ghost coders, it’s essential to take a panoramic view of their journey. From the dawn of the digital age to the present, and even projecting into the future, the evolution of these anonymous figures tells a broader story of technology, society, and the eternal game of cat and mouse.
The Humble Beginnings
- Early Hackers and Phreakers: In the 1970s and 1980s, the world saw the emergence of the first hackers and phreakers, enthusiasts who manipulated phone systems. Their motivations were often more about exploration and curiosity than malice.
- Bulletin Board Systems (BBS): Before the widespread use of the internet, BBSs were the primary means of digital communication. These systems became the breeding grounds for early digital communities, where knowledge about hacking started to spread.
The Rise of Infamy
- The Morris Worm: In 1988, one of the first recognized computer worms propagated through the nascent internet. Created by Robert Tappan Morris, it unintentionally caused significant damage, marking a turning point in public perception of hacking.
- High-Profile Attacks: As the internet grew in the 1990s and 2000s, so did the visibility and impact of cyber attacks. Incidents like the Love Bug virus and breaches at major corporations thrust ghost coders into the spotlight.
The Modern Landscape
- State-Sponsored Entities: Today, the line between individual hackers and state actors is increasingly blurred. Nations have recognized the potential of cyber warfare and espionage, often employing or backing skilled coders for strategic purposes.
- Ransomware Reign: The 2010s saw a significant rise in ransomware attacks, with ghost coders targeting hospitals, cities, and corporations, turning data encryption into a lucrative business.
Peering into the Future
- AI and Machine Learning: As artificial intelligence and machine learning technologies mature, they might become the new tools in the arsenal of ghost coders, enabling more sophisticated and autonomous attacks.
- Quantum Computing: The advent of quantum computers poses a potential threat to traditional encryption methods. Ghost coders might harness this power to crack previously unbreakable codes, or conversely, to create even more secure malware.
- Decentralized Web: As concerns about privacy and control lead to a push for a decentralized internet, new opportunities and challenges will arise. Ghost coders may find new avenues to exploit or face more fragmented and resilient systems.
Morphing in the Digital Tide: The journey of ghost coders is emblematic of the broader evolution of the digital age. As tools, technologies, and motivations shift, these shadowy figures will continue to adapt, ensuring that the world of cybersecurity remains dynamic and ever-challenging.
Deciphering the Digital Enigma: Ghost Coders in Perspective
The intricate web woven by ghost coders serves as a mirror to our increasingly interconnected world. It reflects both the vulnerabilities of a society heavily reliant on digital systems and the astonishing power of individuals operating from the shadows. Yet, beyond the code, ransomware, and breaches, the narrative of ghost coders is deeply human. It speaks to age-old themes of curiosity, ambition, defiance, and the eternal struggle between security and freedom.
Our response to these figures, as individuals and as a society, will define the next chapter in the digital age. It isn’t just about creating stronger firewalls or implementing better security protocols. It’s about understanding the motivations that drive these anonymous figures, addressing the root causes, and fostering a digital environment where creativity flourishes without causing harm.
As we stand at the crossroads, the challenge is twofold. First, to fortify our digital domains against the threats posed by these phantom coders. And second, and perhaps more importantly, to engage in a broader discourse about the kind of digital world we envision for the future—a world that’s safe, inclusive, and respectful of individual rights.
In the dance of shadows and light, of codes and ciphers, the story of ghost coders is a testament to the transformative power of technology and the enduring complexities of the human spirit. As we navigate this journey, it’s our collective responsibility to ensure that the digital age evolves in harmony with our highest ideals and aspirations.
Facing Cybersecurity Concerns? Digital Parameters Has Your Back!
While the mysterious world of ghost coders might seem distant and elusive, the repercussions of their actions can touch businesses of all sizes, especially in the ever-evolving digital realm. Safeguarding your online presence and maximizing your digital potential is more crucial than ever.
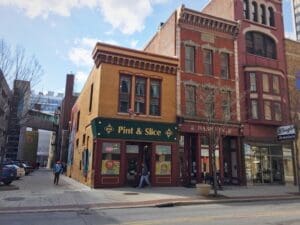
Digital Parameters – Fort Wayne’s premier SEO & Web Design agency – stands at the forefront of creating robust digital solutions. Recognized as the best Digital Marketing Agency in Fort Wayne by Expertise and Design Rush, we are dedicated to providing unparalleled services tailored just for you:
- Need a striking online presence? Dive into our Website Design offerings.
- Want to rank high on search engines? Explore our renowned SEO services.
- Looking to expand your eCommerce reach? We’ve got holistic eCommerce Solutions.
- Navigating the world of online advertising? Tap into our Google Ads and Facebook Ads expertise.
- Wishing to streamline your online operations? Check out our Website Management suite.
With over two decades of experience, Digital Parameters is more than just an agency; we’re your partner in crafting a digital success story. Whether you’re based in Fort Wayne, Indiana, or beyond, we’re equipped to transform your online trajectory.
Take Action Now! Don’t let concerns related to the digital world hold you back. Reach out to Digital Parameters today and embark on a journey of growth, security, and unparalleled success. With us by your side, your digital fortress stands resilient and thriving.